Configure Your Galaxy Instance as an OIDC Client of ELIXIR Authentication and Authorisation Infrastructure
On this page
This page explains how to configure this feature, for user-specific docs, please refer to this page.
Leveraging OpenID Connect (OIDC) protocol, users can login to Galaxy using their identity on ELIXIR Authentication and Authorisation Infrastructure (AAI), without having to (explicitly) create a Galaxy user account. To enable this feature on your Galaxy instance, you would need to first register you Galaxy instance as an OIDC relying party (RP, or client) with ELIXIR AAI, and then use your registration information to configure Galaxy. These steps are described in details in the following sections.
Client Registration
Take the following steps to register your Galaxy instance (RP) to the ELIXIR AAI test environment:
-
Create an ELIXIR identity, if you do not already have it.
-
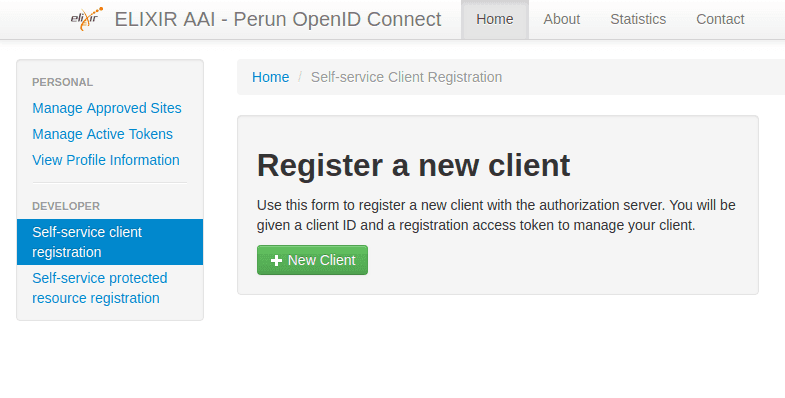
Click here to start register your client and you’ll see a dashboard as the following:
-
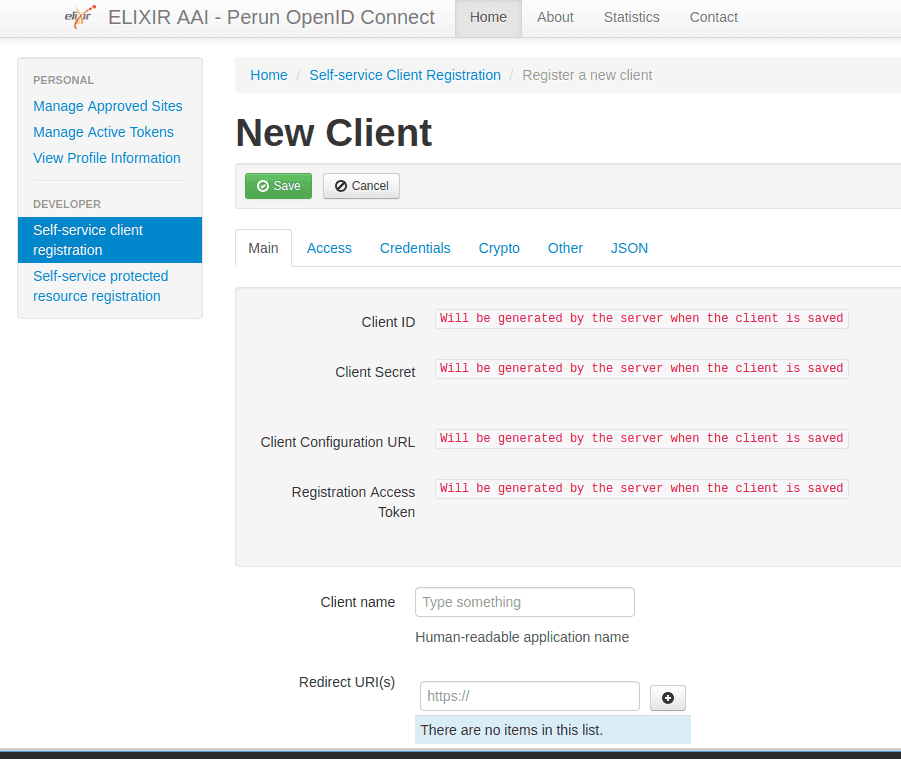
Click the green “New Client” button:
-
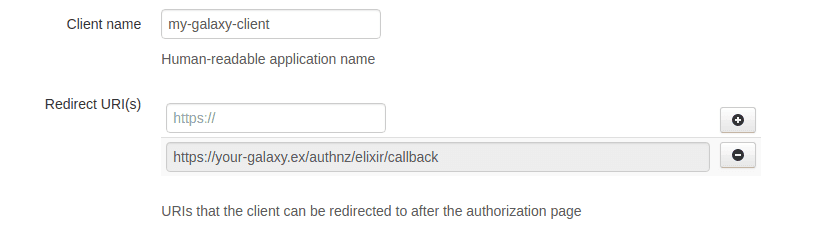
Fill in the “Client name” and “Redirect URI” fields, and all the other fields are optional.
-
Click the green “Save” button at the bottom (or at the top) and make a note of all the generated credentials that is made available to you. The
Client IDandClient Secretfields will be used to configure Galaxy, andClient Configuration URLandRegistration Access Tokenwill be needed to access the client registration in future.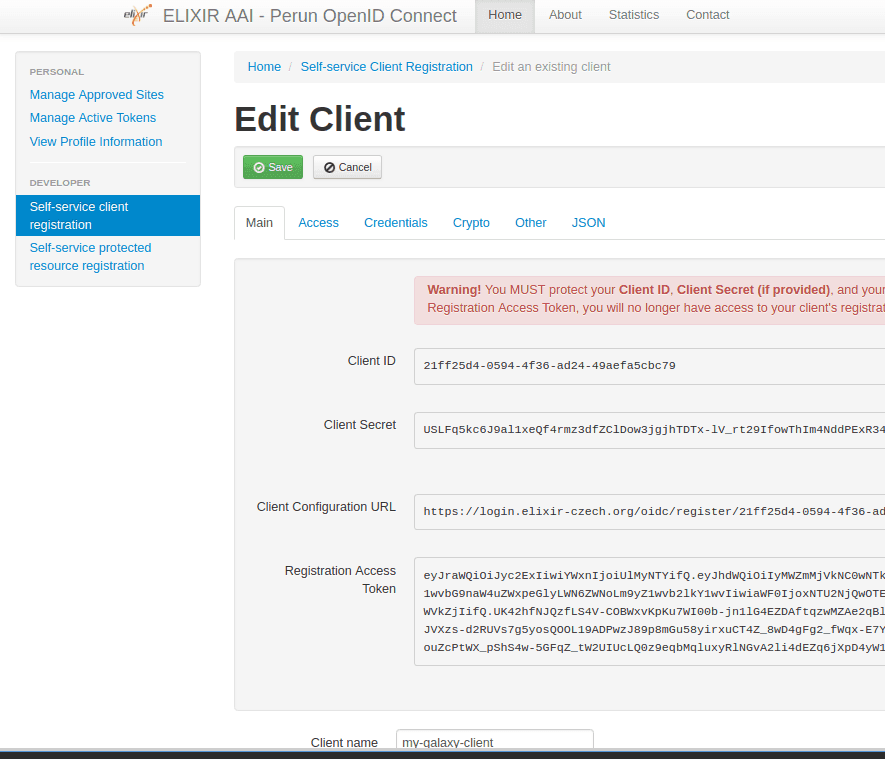
-
Drop the following information by e-mail to aai-contact@elixir-europe.org:
-
Name of your service
-
Description of your service
-
Your service’s Client_id
-
-
Wait for a reply from ELIXIR AAI with a form for you to complete. It includes requesting which attribute scopes should be returned to Galaxy when users authenticate. We recommend to only request openid and email scopes, as this is the minimum that is needed and will be utilized by Galaxy.
-
Return the pre-filled form and when accepted, the ELIXIR AAI service is ready to receive authentication requests from your Galaxy server! Of course you also need to configure your Galaxy first, so read on under Galaxy Configuration.
Without the complition of steps **7** and **8**, your Galaxy instances can NOT verify users
authentication based on the information it receives from ELIXIR AAI, because this
provider does not provide a client with all information required as per OIDC
specifications (e.g., `id_token`) by default. The ELIXIR AAI - Manual for Service Providers provides more details on the client registration process. The steps discussed here leads to registering a Galaxy instance to the ELIXIR AAI test environment. However, for production deployment, you would need to promote your service from the test environment to the prod environment following the described administrative procedures in Step 3 of the ELIXIR AAI - Manual for Service Providers.
Galaxy Configuration
You would need to setup your Galaxy instance to leverage OIDC protocol.
This setup is common for all OIDC IdPs, and is
documented at this page.
Then you would need to add ELIXIR AAI-specific setters to the config/oidc_backends_config.xml
matching the values you got from the client registration process, as well as the exact same
redirect_uri you specified (depending on your setup):
<?xml version="1.0"?>
<OIDC>
<provider name="Elixir">
<client_id> ... </client_id>
<client_secret> ... </client_secret>
<redirect_uri>http://localhost:8080/authnz/elixir/callback</redirect_uri>
<prompt>consent</prompt>
</provider>
</OIDC>Having set this configuration, restart Galaxy to have the option of login to Galaxy with ELIXIR AAI identity: